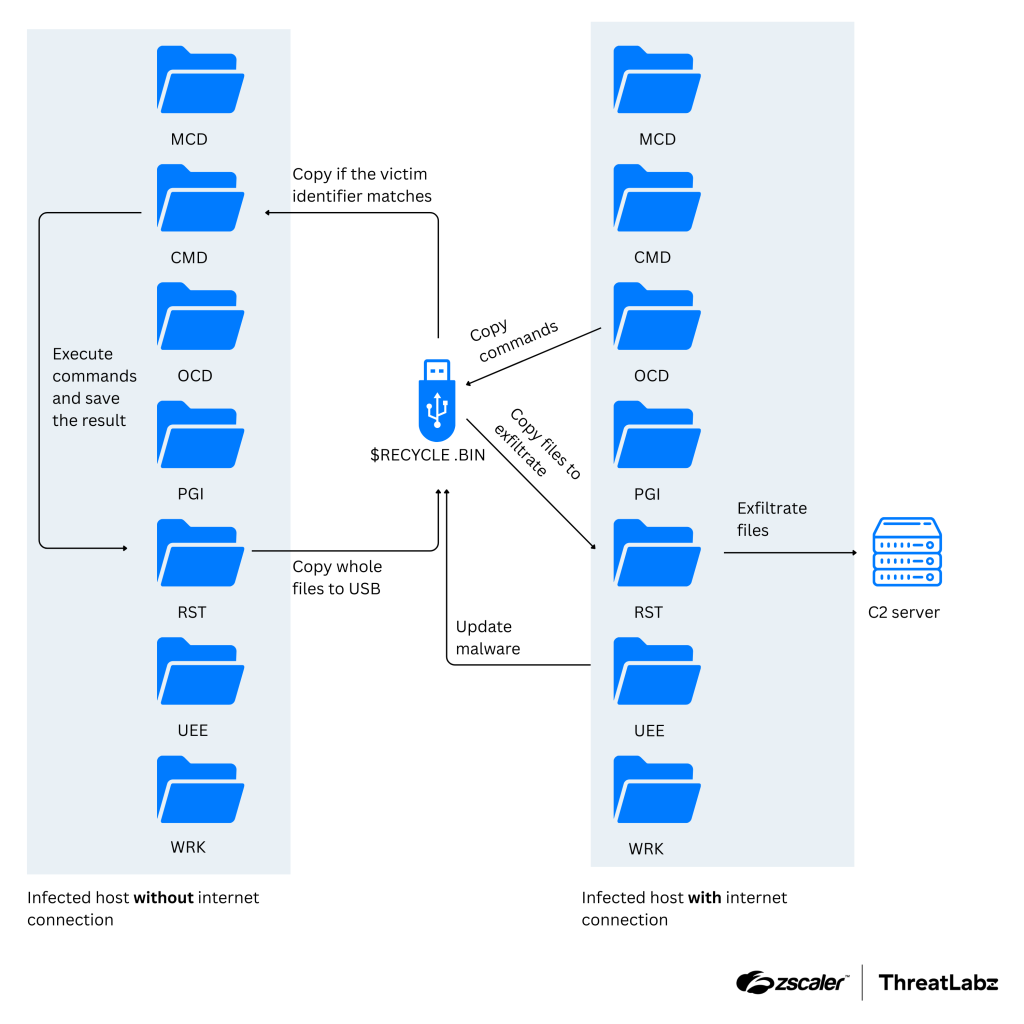
APT37 combines cloud storage and USB implants to infiltrate air-gapped systems
North Korea-linked APT 37 used Zoho WorkDrive and USB malware to breach air-gapped networks in the Ruby Jumper campaign. North Korean group ScarCruft (aka APT37, Reaper, and Group123) deployed new tools in a campaign dubbed Ruby Jumper, using a backdoor that …
APT37 combines cloud storage and USB implants to infiltrate air-gapped systems North Korean group ScarCruft (aka APT37, Reaper, and Group123) deployed new tools in a campaign dubbed Ruby Jumper, usi… [+4186 chars]