The preparations for HOPE 26 are in full swing! Tickets are still available here and cheap hotel rooms in midtown Manhattan can be found at this link (if rooms aren't available, try back in a few hours as demand is high and our supply is frequently being repl…
The preparations for HOPE 26 are in full swing! Tickets are still available here and cheap hotel rooms in midtown Manhattan can be found at this link (if rooms aren't available, try back in a few hou… [+2802 chars]
What’s the latest brick in Russia’s effort to build its Great Internet Firewall? A proposal to create a government-run Virtual Private Network, co-opting a tool that has been widely embraced by Russians trying to avoid government censorship. Industry insiders…
Since the onset of all-out war on Ukraine in February 2022, Russian authorities have dropped a veil of censorship -- both overt and covert -- on news, dissent, and debate about the conflict, not to m… [+6068 chars]
Telenor has agreed to acquire Enivest, one of the leading fibre operators in Western Norway, in a transaction valued at NOK 2.5 billion...
(Fornebu, 10 June 2026) Telenor has agreed to acquire Enivest, one of the leading fibre operators in Western Norway, in a transaction valued at NOK 2.5 billion.
The acquisition includes Enivests fib… [+3413 chars]
Access alone is not enough. Technology is only useful if people trust it, understand how to use it safely, and can rely on support networks when digital spaces become unstable or dangerous. ASL19's Paskoocheh helps people in Iran access trusted privacy and ci…
++ This guest post is part of a spotlight series on the organizations defending the free Internet.++
Due to heavy information controls, people in Iran face significant barriers to accessing the Int… [+6418 chars]
Rossiya Segodnya media group hosted an international session titled Next-Generation Media: Responding to Global Challenges on the sidelines of the St. Petersburg International Economic Forum (SPIEF).
Get the latest news from around the world, live coverage, off-beat stories, features and analysis.
https://sputnikglobe.com/20260609/challenges-of-the-modern-media-industry-discussed-at-spief-112428… [+4324 chars]
There was more to it than the loss of its CEO and legal pressure from IBM
When it comes to 80s computer brands, few flew as high as Eagle Computer flew in 1983. The aptly named company was selling 12,000 computers a month and had been doubling sales every quarter under the… [+16537 chars]
The Estonian Police and Border Guard Board has begun the issuance of the country’s new electronic identity (eID) cards, marking a major milestone in the ongoing modernisation of Estonia’s renowned digital identity programme. This new generation of cards has b…
<ul><li>The Estonian Police and Border Guard Board has begun the issuance of the countrys new electronic identity (eID) cards, marking a major milestone in the ongoing modernisation of Estonias renow… [+7109 chars]
On July 1, 2026, Hansjörg Herrbold and Andreas Hägele will take over as Executive Vice Presidents Technology Systems at Rohde & Schwarz. They follow Dr. Luis Alejandro Orellano, who will leave the company on June 30 at his own request. The decision to establi…
On July 1, 2026, Hansjörg Herrbold and Andreas Hägele will take over as Executive Vice Presidents Technology Systems at Rohde & Schwarz. They follow Dr. Luis Alejandro Orellano, who will leave th… [+1768 chars]
Has asked court to hold spyware vendor in contempt.
Meta has accusedNSO Group of continuing to target its WhatsApp communications app despite widespread publicity and official and legal sanctions against the spyware vendor.
WhatsApp said it caught an… [+1305 chars]
WISeKey, The Hashgraph Group and Hedera Launch QAIT Q-Day Security Assessment Platform on the SEALCOIN Quantum Marketplace First Quantum Security...
WISeKey, The Hashgraph Group and Hedera Launch QAIT Q-Day Security Assessment Platform on the SEALCOIN Quantum Marketplace
First Quantum Security Service to Launch Within SEALCOINs Dedicated Quantum… [+12515 chars]
Reports of an organised crime gang that looted luxury homes across the UK by studying their floorplans on Rightmove is a stark reminder that the traditional image of a burglar is outdated.
Recent reports of an organised crime gang that looted luxury homes across the UK by studying their floorplans on Rightmove is a stark reminder that the traditional image of a burglar is outdated.
T… [+10096 chars]
At 8:30 in the evening on Wednesday 2 November 1988, a 23-year-old graduate student named Robert Tappan Morris, in his first semester of a PhD programme in computer science at Cornell University, logged into a Massachusetts Institute of Technology computer fr…
At 8:30 in the evening on Wednesday 2 November 1988, a 23-year-old graduate student named Robert Tappan Morris, in his first semester of a PhD programme in computer science at Cornell University, log… [+7846 chars]
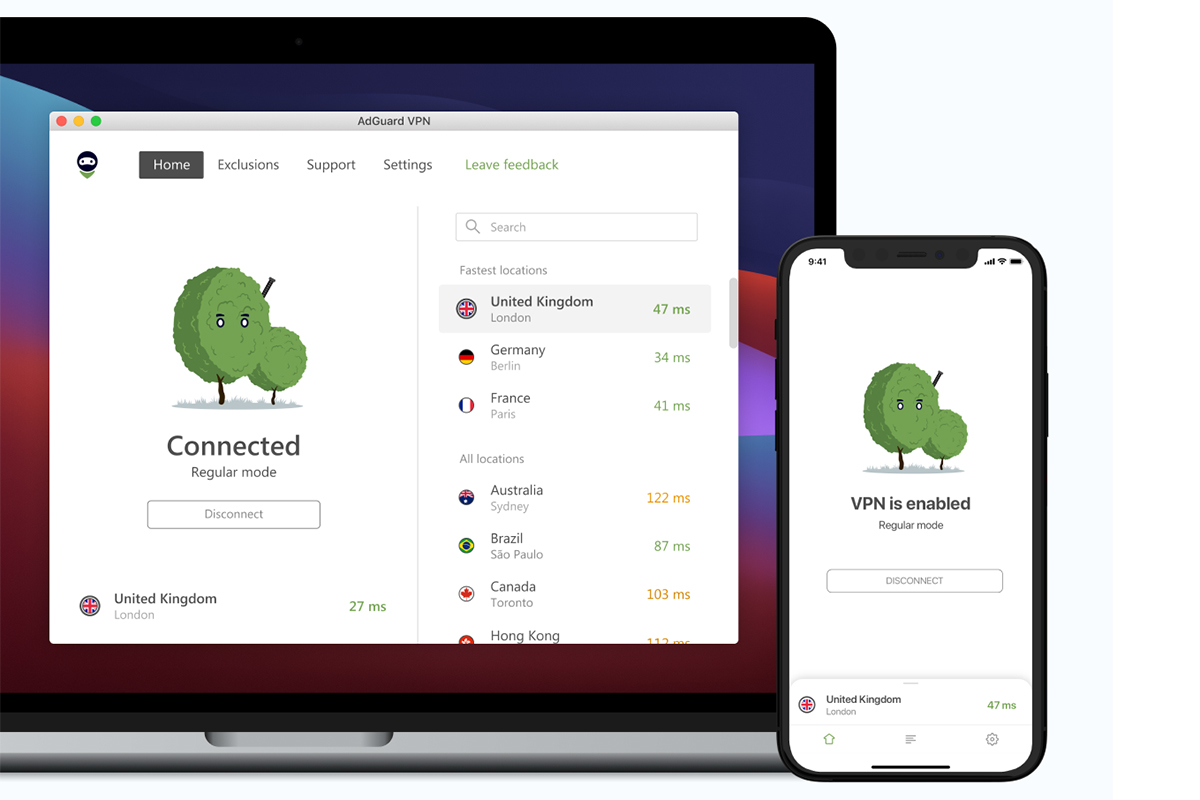
Fast, private browsing and family-wide protection in one discounted bundle.
The post Safeguard your family with AdGuard VPN & the Security Suite for $35 appeared first on Popular Science.
We may earn revenue from the products available on this page and participate in affiliate programs. Learn more TL;DR: AdGuard VPN and the Family Plan provide a combined approach to online safety, so … [+2430 chars]
Spending extra on a good VPN service is a net benefit that’ll always pay off in the backend. But with this $49.99 (reg. $89.95) 1-year subscription to the ExpressVPN Advanced Plan, you can cut costs without any of the fallout. Better yet, your subscription gi…
Spending extra on a good VPN service is a net benefit thatll always pay off in the backend. But with this $49.99 (reg. $89.95) 1-year subscription to the ExpressVPN Advanced Plan, you can cut costs w… [+2454 chars]
Ciena reports blockbuster fiscal Q2 but stock slumpsSK Telecom joins Anthopic’s Project GlasswingFoxconn gets jiggy with Intel and SK Group
In today’s industry news roundup: Despite beating sales and margin expectations and raising its annual revenues forecast, Ciena’s stock has dropped off a cliff; SK Telecom becomes the latest telco to… [+7979 chars]
“In the age of misinformation, the line between fact and fiction is blurrier than ever.” “For those of us working in video news, verification isn’t a nice-to-have. It’s a necessity. It is how we protect the stories we help shape and how we earn and maintain t…
“In the age of misinformation, the line between fact and fiction is blurrier than ever.
For those of us working in video news, verification isnt a nice-to-have. Its a necessity. It is how we protect… [+14334 chars]
The digital threats faced by defenders of truth and democracy are multiplying. So should the capacity to respond to them. Through tools like Ricochet Refresh and cybersecurity training across lower- and middle-income countries, Blueprint for Free Speech helps…
++ This guest post is part of a spotlight series on the organizations defending the free Internet.++
Fear of digital surveillance breeds silence.
In the words of a youth activist in Zambia who t… [+6597 chars]
Tern Orox Technology Shines with the Bosch Flow App It turns out the Tern Orox into something more than an eBike. The Tern Orox is…
The post Tern Orox Technology Shines appeared first on Bike Hugger.
It turns out the Tern Orox into something more than an eBike. The Tern Orox is already one of the most interesting bikes on the market. Its a cargo bike, an adventure bike, a car replacement, and a b… [+4540 chars]
MUMBAI, India, June 03, 2026 (GLOBE NEWSWIRE) -- Fairplay today announced the implementation of an enhanced user verification framework and updated account security measures designed to align with India's evolving 2026 online gaming regulatory requirements. T…
MUMBAI, India, June 03, 2026 (GLOBE NEWSWIRE) -- Fairplay today announced the implementation of an enhanced user verification framework and updated account security measures designed to align with In… [+5531 chars]
Forget about email hackers. What if someone nabs your external drive and all the data on it? Thwart thieves with a drive with strong encryption and security features. We've tested loads of them.
A Guide to Hardware-Based Drive EncryptionEncryption is the proc…
It could be an accident, it could be theft: It's just too easy for the data on an unsecured external hard drive or SSD to fall into the wrong hands. To keep your data safe, consider an encrypted exte… [+8227 chars]
French President Emmanuel Macron has looked to win over tech bosses amid hopes to boost AI capability.
OpenAI chief Sam Altman will be attending the G7 conference in France later this month, CNBC has learned, as President Emmanuel Macron steps up efforts to court tech leaders across the globe in suppo… [+3021 chars]
Public skill marketplaces are being flooded with malicious skills that steal credentials, exfiltrate data, and hijack agents. In response, a segment of the security industry released skill scanners, a new family of tools designed to detect malicious skills be…
Public skill marketplaces are being flooded with malicious skills that steal credentials, exfiltrate data, and hijack agents. In response, a segment of the security industry released skill scanners, … [+19867 chars]
Anthropic had announced on Tuesday that it gave approximately 150 organisations around the world access to its AI model Mythos, whose ability to rapidly identify weaknesses in computer security has sparked global concern about vulnerabilities.
Claude-maker Anthropic said it will provide access to its powerful Mythos model to companies and institutions in more than 15 countries, including India, the Financial Times reported.Anthropic had an… [+1285 chars]
Working with AI world leaders at CommBank’s San Francisco Tech Hub offers CommBank’s technologists the opportunity to learn at the frontier in the world’s leading technology ecosystem.
Technologists at the new San Francisco Tech Hub learn from partners such as OpenAI and Anthropic to support adoption of emerging AI technologies. It builds on CommBank’s Seattle Tech Hub, where more … [+5694 chars]
Anthropic has opened access to its new AI model, Mythos, to 150 organisations worldwide. This powerful AI can rapidly find computer security flaws. Early tests revealed thousands of vulnerabilities. Now, groups from over 15 countries, including critical infra…
Anthropic on Tuesday gave approximately 150 organisations around the world access to Mythos, its powerful new AI model whose rapid ability to identify weaknesses in computer security that has sparked… [+2372 chars]