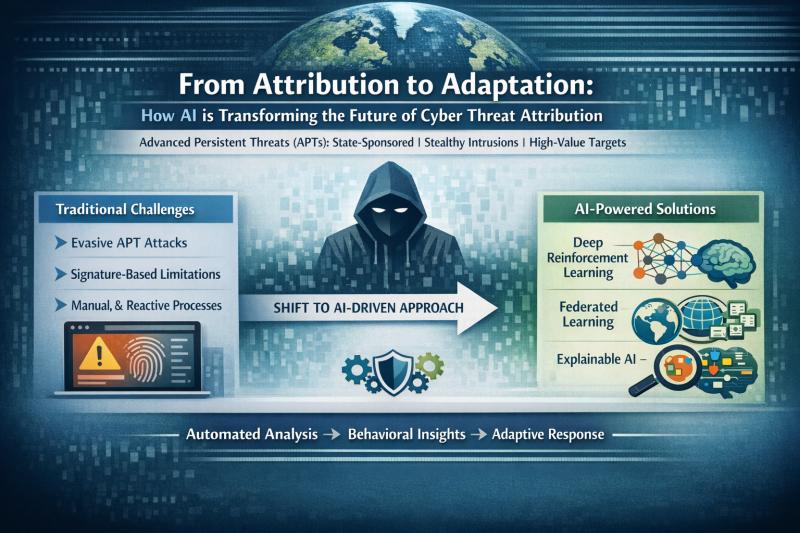
From Attribution to Adaptation: How AI is Transforming the Future of Cyber Threat Attribution
Advanced Persistent Threats (APTs) are long‑term, highly sophisticated attacks carried out by well‑resourced or state‑sponsored actors who infiltrate networks, evade detection for months, and target high‑value information. Traditional signature‑based cybersecurity tools can no longer keep up with these stealthy campaigns, making attribution far more complex and reliant on behavioral and intelligence‑driven methods. In this blog, we explore how AI—particularly Deep Reinforcement Learning, Federated Learning, and Explainable AI—is transforming APT attribution from a manual, reactive process into an automated and adaptive capability.
Introduction
Advanced Persistent Threats (APTs) have become one of the most sophisticated and stealthy forms of cyberattack in the modern digital world. Unlike opportunistic malware or one-off intrusions, APT campaigns are orchestrated by well-resourced, often state-sponsored actors who patiently infiltrate networks, evade detection for months, and extract high-value information. Traditional cybersecurity tools rely on signature-based detection, malware hashes, or blacklisted IPs and are no longer sufficient to keep pace with this adversarial sophistication. As a result, cyber attribution, the process of identifying who is behind an attack, has evolved from a purely forensic task into a complex problem requiring behavioral analysis, intelligence fusion and AI-driven decision-making.
In this blog, we explore how Artificial Intelligence (AI), especially Deep Reinforcement Learning (DRL), Federated Learning (FL), and Explainable AI (XAI), is reshaping the future of APT attribution. This shift is enabling us to move from manual, reactive attribution to automated, adaptive systems.
Cyber Attribution: Looking Beyond Hashes and IP Addresses
Cyber attribution is rarely a simple task; it operates on three distinct conceptual levels:
-
Technical Attribution: Identifying the low-level Indicators of Compromise (IoCs) like tools, malware families, and network artifacts.
-
Tactical Attribution: Recognizing the Tactics, Techniques, and Procedures (TTPs) used in the attack.
-
Strategic Attribution: Inferring the adversary's motivations, geopolitical context and organizational backing.
In modern attacks, relying solely on IoCs is insufficient. IPs can be spoofed, malware hashes mutate rapidly, and widely used tools like Mimikatz appear across many different threat groups. None of these indicators reliably point to a specific actor. Meaningful attribution must now rely on behavioral correlation, examining how attackers behave rather than just what files they drop or what tools they use. Groups such as APT1 (China), APT28 (Russia), MuddyWater (Iran), and Lazarus Group (North Korea) are often distinguished by patterns that analysts learn over time, such as their command-and-control communication (C2) cadence, privilege-escalation methods, persistence techniques, and lateral movement style. These consistent behavioral traits form the foundation of modern attribution models.
Why APT Attribution is Hard and Why We Need AI
The shift to AI is essential because our current approach is fundamentally fragile. Traditional attribution is a slow, manual chore that demands deep, specialized human expertise that simply isn't available on a scale. Crucially, these old workflows cannot generalize across diverse and rapidly evolving attacker behaviors and malware types; they break every time an attacker introduces a new trick or a variant malware. Earlier, classical models like Support Vector Machines (SVMs) and Random Forests were used effectively, but the field is now progressing rapidly toward more advanced techniques. Recent literature highlights a clear evolution in attribution techniques:
-
Static Models: Good for early detection but struggle with evolving behavior.
-
Sequential/Temporal Models: Better capture the behavioral progressions of an attack.
-
Reinforcement Learning (RL)/DRL Models: Designed to adapt to attacker strategies over time.
A 2025 survey by Rani et al. showed that Deep Reinforcement Learning (DRL) has emerged as a highly promising method because it learns attribution strategies directly from interactions, making it resilient to obfuscation and evolving TTPs. Given this evidence, it is worth examining how DRL reframes the attribution problem.
Deep Reinforcement Learning (DRL): A New Paradigm
Reinforcement Learning reframes attribution as a dynamic decision-making problem. To understand why DRL fits this problem so naturally, it helps to map its core components to the elements of malware-behavior analysis, as shown in Table 1.
|
DRL Component |
APT Attribution Equivalent |
|---|---|
|
Agent |
The AI classifier |
|
Environment |
Sandbox-generated behavioral logs |
|
State |
API calls, registry writes, file modifications, network patterns |
|
Action |
Selecting which APT group a sample belongs to |
|
Reward |
Based on correct or incorrect predictions |
This alignment highlights why DRL is increasingly favored: attribution is not a static classification task, but a sequence of behavioral observations in which the model must infer which threat actor is most likely responsible. In practice, sandboxing tools such as Cuckoo Sandbox generate rich behavioral reports including API sequences, process trees, and registry manipulations, providing ideal state representations for DRL models.
In one study (Basnet et al., 2025), DRL demonstrated 6-18% higher accuracy than classical machine learning across a dataset of 3,594 malware samples from 12 APT groups. Critically, DRL also showed stronger generalization to previously unseen samples, a massive advantage against stealthy, constantly innovating actors. While these results are encouraging, deploying DRL in real-world attribution pipelines introduces several significant challenges that need to be addressed.
Addressing the Challenges
Despite its promise, DRL faces several practical limitations that become clear when moving from controlled research settings to real-world attribution systems:
-
Heavy Computational Demand: DRL models require thousands of training episodes and powerful GPUs, creating a major bottleneck for organizations lacking advanced infrastructure.
-
Privacy Concerns: Attribution often requires collaboration between Security Operation Centers (SOCs), enterprises and government agencies. However, raw malware logs and system telemetry are too sensitive to share directly.
-
Lack of Explainability: Analysts and decision-makers need to understand why a model attributed malware to a particular group. Transparent reasoning is crucial, especially in high-stakes geopolitical contexts.
These challenges may seem substantial, but recent research has introduced practical strategies to mitigate them.
- Federated Learning (FL): FL allows multiple organizations to build a global threat intelligence model without sharing sensitive raw data. Instead of pooling all sensitive logs into one server:
- Each SOC trains a local model.
- Only the model parameters (updates) are shared.
- A robust global model is collaboratively built.
This approach preserves privacy while ensuring the training data is broad and representative.
- Explainable Federated Learning (XFL): Building on FL, frameworks like XFedHunter combine federated model training with XAI techniques such as SHAP values. This provides:
- Privacy-preserving multi-organizational attribution.
- Human-interpretable explanations of the attribution decision.
- Insights into which behavioral features most influenced the outcome.
These AI-powered techniques help to balance privacy and transparency, especially because attribution extends far beyond the technical domain into geopolitical and legal arenas.
The Road Ahead: Adaptive and Ethical Attribution
The field is changing rapidly, not because AI has magically evolved, but because we finally have the data, infrastructure and computational power to apply these methods in a meaningful way. As a result, attribution is becoming not just more adaptive, but more aligned with ethical and privacy expectations. The next generation of systems will depend heavily on cross-organizational cooperation and on transparent explanations that analysts can trust when decisions carry geopolitical or legal weight.
Going forward, attribution systems are likely to incorporate:
-
Cross-organizational collaboration without compromising privacy.
-
Hybrid models that combine DRL with temporal graph networks and LLM-based reasoning to capture evolving attacker behavior.
-
Adaptive learning loops that improve as attacker behaviors evolve.
-
Transparent explanations to support decisions at every level, from SOC analysts to government agencies.
As AI-driven methods mature, attribution is gradually shifting from a static, post-incident task to a dynamic and collaborative process that can respond in real time to how modern threat actors operate.
Edited By: Windhya Rankothge, PhD, Canadian Institute for Cybersecurity
References
-
Rani, N., Saha, B., & Shukla, S. K. (2025). A comprehensive survey of automated Advanced Persistent Threat attribution: Taxonomy, methods, challenges and open research problems. Journal of Information Security and Applications, 92, 104076. https://doi.org/10.1016/j.jisa.2025.104076
-
S. Basnet, M. C. Ghanem, D. Dunsin, H. Kheddar, and W. Sowinski-Mydlarz (2025). Advanced Persistent Threats (APT) Attribution Using Deep Reinforcement Learning. Digital Threats, 6(3), Article 14, 23 pages. https://doi.org/10.1145/3736654
-
H. T. Thi, N. D. H. Son, P. T. Duy, N. H. Khoa, and K. Ngo-Khanh (2023). XFedHunter: An Explainable Federated Learning Framework for Advanced Persistent Threat Detection in SDN.arXiv:2309.08485. https://arxiv.org/abs/2309.08485
-
A. Javadpour, F. Ja'fari, T. Taleb, M. Shojafar, and C. Benzaïd (2024). A comprehensive survey on cyber deception techniques to improve honeypot performance. Computers & Security, 140,103792. https://doi.org/10.1016/j.cose.2024.103792