
Review: The Amazing Digital Circus: The Last Act
The Amazing Digital Circus: The Last Act is a massive milestone for indie animation, but does it stick the landing? Our spoiler-free review:

The Amazing Digital Circus: The Last Act is a massive milestone for indie animation, but does it stick the landing? Our spoiler-free review:

The ShinyHunters hacking gang claims to have compromised the Oracle PeopleSoft servers of more than 100 organizations, including many universities.

I thought I couldn't be any more impressed with Onimusha: Way of the Sword, but after a recent Summer Game Fest demo, I'm convinced Capcom is cooking up another game-of-the-year candidate. LOS ANGELES—It's been roughly a year since I first played the Onimusha…

A covert botnet linked to Chinese state-sponsored hackers has more than doubled in size and is now scanning for newly disclosed vulnerabilities within hours of publication. The JDY botnet comprises over 1,500 compromised small office and home office routers, …
India has effectively frozen the approvals Starlink needs to begin commercial operations in the country. Security agencies under India’s Ministry of Home Affairs withheld final clearances after SpaceX allowed Starlink access inside Iran despite not having a l…

CEOs must embrace AI leadership to unlock transformative potential akin to the invention of electricity. The post Pedro Franceschi: CEOs must become chief AI officers, misconceptions about LLMs limit innovation, and reasoning models are pivotal for AI’s evolu…

The JDY botnet has expanded to over 1,500 compromised devices to conduct large-scale reconnaissance and service fingerprinting. This network primarily targets small office and home office routers, firewalls, and IoT devices from various manufacturers. It func…

The Indian government got cold feet on Starlink just before SpaceX's IPO | TechCrunchtechcrunch.com

Hackers breached Instagram’s defenses last month due to an artificial intelligence chatbot vulnerability, The New York Times reported Tuesday (June 9). In all, 34,000 accounts on the Meta-owned social media site were affected, according to the report, which c…

Some cool ideas don't make this open-world action-shooter worth playing

The Financial Stability Board is calling on financial institutions to create safeguards against AI-related risks. In a report published Wednesday (June 10), the FSB said it was “strongly” encouraging these companies to consider establishing measures to offset…

Hello folks, and welcome back to Wrong Every Time. It’s been a productive week on my end, as I’ve been keeping up my jogging routine, hacking away at the new book, and sampling a variety of new productions courtesy of … Continue reading →

MSP platform expansion is purpose-built for partners navigating the next wave of enterprise AI REDWOOD CITY, Calif., June 10, 2026 /PRNewswire/ -- Check Point® Software Technologies Ltd. (NASDAQ: CHKP), a pioneer and global leader of cyber security solutions,…

Residential proxy services route internet traffic through consumer devices to make connections appear as if they originate from legitimate home IP addresses. Recent research reveals that these services have penetrated over 65% of enterprise, government, and f…

A cybercrime group known as The Gentlemen has emerged as the second most active ransomware gang by victim count, rapidly attracting a talented pool of hackers through an aggressive recruitment strategy that promises affiliates 90 percent of any ransom paid by…

Courtesy of Bandai Namco The reveal of Gundam Rogue Orbit also showed off heavy mech action in its gameplay, where players use special skills and melee attacks to take on dangerous enemies. From small groups to large bosses, it looks like this game will rely…
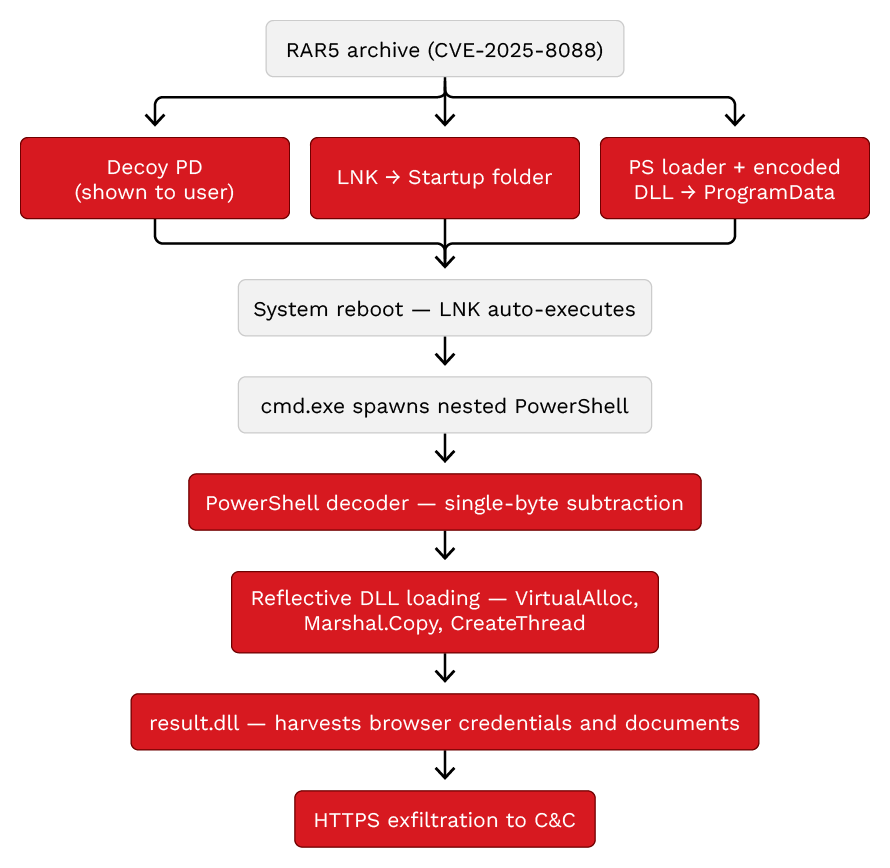
Despite a 2025 patch, Russian-linked groups still exploit a WinRAR flaw (CVE-2025-8088) to deploy malware via phishing archives. CVE-2025-8088 is a path traversal flaw in WinRAR that lets an attacker write files outside the extraction directory using NTFS Alt…

The measure would require CISA to refresh long-outdated sector cybersecurity plans as lawmakers warn that advanced AI tools could accelerate the discovery and exploitation of software flaws.

The industrial landscape is evolving at an incredible pace. As IT and OT environments continue to converge, the traditional boundaries of network security are shifting, creating both new challenges and significant professional opportunities.

Wednesday’s lineup of the best iOS game and app deals is now ready to roll, including titles like Northgard, Little Big Workshop, The Quest – Islands of Ice and Fire, Lia: Hacking Destiny, Rotaeno, and more. We also have up to $300 off M5 Pro MacBook Pro mode…
Introduces new ZAgent Framework for agentic administration, and extends SASE to unmanaged devices, B2B partners, and multi-cloud workloads Introduces new ZAgent Framework for agentic administration, and extends SASE to unmanaged devices, B2B partners, and mul…

AUSTIN, Texas, June 10, 2026 /PRNewswire/ -- Scale Computing™, the leader in edge computing and network solutions, today announced the company has earned 41 badges in the G2 Summer 2026 Reports, including Leader in the G2 Grid® Report marketplace evaluation. …

U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Cisco Catalyst SD-WAN, Arista Extensible Operating System (EOS), and Google Chromium V8 flaws to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Security …

Instagram's long-dormant White House account for former President Barack Obama recently came roaring back to life, complete with bizarre, out-of-the-norm posts about President Trump and ones that insisted the White House was "under Shiite control." Per the Ne…
WhatsApp has caught the NSO Group phishing its users, in violation of a court order.